Submission - Joint submission to the 2007 Review of the Electronic Funds Transfer (EFT) Code of Conduct to ASIC (May 2007)
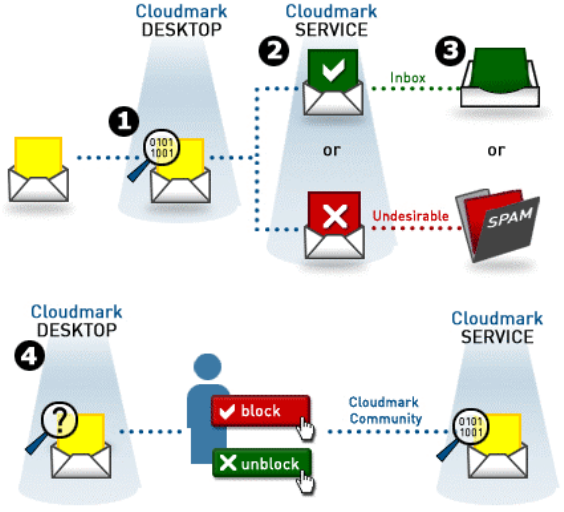
Cloudmark Network Feedback System
Since phishing emails that attempt to lure users to spoofed websites will often be sent out to multiple recipients, if one recipient recognises that the email is fraudulent in nature there have been suggestions that they should be able to effectively communicate that information to other Internet users.[57]
An example of a collaborative technology which gives effect to these suggestions is provided by the Cloudmark Network Feedback System (CNFS), which allows users from around the world to report when they have received what they perceive as a phishing email. Fingerprints for each of these emails is generated using specific algorithms. Once a certain number of users (the number may vary depending on the trust rating of the various users who have made a report to Cloudmark) have identified a specific fingerprint as belonging to a ‘phishing’ email, all messages with the same fingerprint are filtered in real-time from the inboxes of other users that are part of the network. The algorithms which generate email fingerprints are flexible enough to accommodate minor changes to the email that may be made by an attacker as part of an attempt to avoid the message being recognised as a phishing email.
[57] Fette I, Sadeh N and Cranor L, Web Security Requirements: A Phishing Perspective, W3C Workshop on Transparency and Usability of Web Authentication, March 2006, <http://www.w3.org/2005/Security/usability-ws/papers/13-cmu-requirements>, page 1.
![[2015 EU Cybersecurity Dashboard]](/public/ssi/pubs/pub_4.png)
 print this page
print this page sitemap
sitemap rss news feed
rss news feed manage email subscriptions
manage email subscriptions