PKI Interoperability Models (February 2005)
4.1. Root CA/Hierarchy Model
The root CA/hierarchy model describes a set of models based on a Root CA and/or a strict hierarchy of certificates.
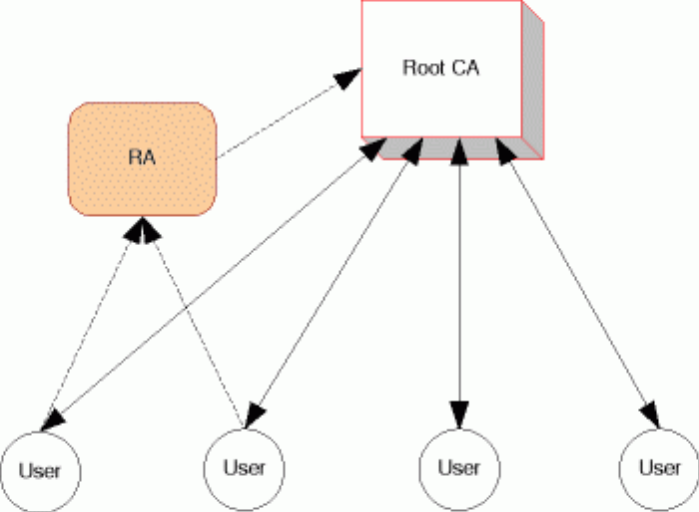
The simplest approach to a PKI framework is to have a single (root) CA. It holds all certificates; all end-users refer to and trust it for all transactions.
The model can include Registration Authorities (RAs) which process the initial identification of users and issue key pairs. This adds some flexibility in the system by allowing for smaller groups to have their own local and customised services.
Figure 1. Root CA Model
This architecture simply avoids the various problems of interoperability and provides a single, convenient point of access. However, it suffers from a number of limitations, especially as the number of users increases:
- The technical and administrative workload of the CA would be enormous for large (country-wide) PKI schemes;
- Different groups of users will have different needs which a single CA cannot address all at once – for example, sensitive applications like health will require advanced and complex procedures, while tax applications will place far more value on speed and efficiency;
- It may be difficult to get all users to accept a single provider; and
- The single CA provides an obvious target for hackers and a security breach affects the entire system.
The root CA model is the basic unit of all PKIs, but it does not provide a useful approach to interoperability. A logical variation is the strict hierarchy model.
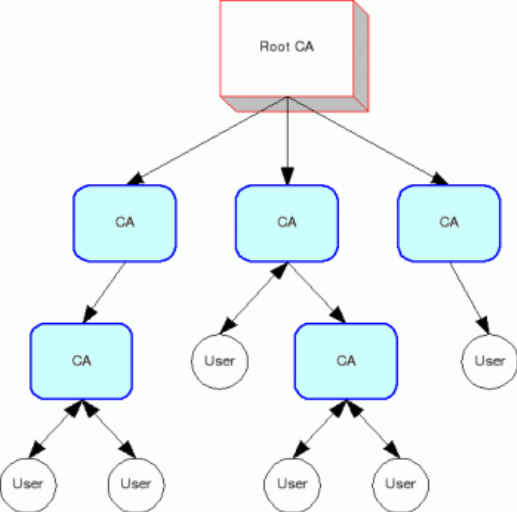
In a strict hierarchy, there is a trusted root CA which issues a certificate to subordinate CAs. Those CAs may, depending on the relevant policy, certify other CAs.
Each CA is trusted because the higher CA that certifies it is trusted. Only the root CA must be trusted on its own.
The hierarchical structure means there is a short and definite path to trace a certificate back to a trusted source, avoiding the more difficult processes of validating a certificate in a flat structure such as a cross-certification mesh (discussed below).
Figure 2. Hierarchy Model
This model adds an extra layer of flexibility to the simple root CA model and allows for competition and specialisation between CAs. However, in practice it suffers from many of the same limitations.
- Participants must be persuaded to subject themselves to the root operator;
- The root CA remains a critical security point; and
- The technical policies imposed by the root may restrict innovation and competition.
The root CA/hierarchical model has advantages in some situations:
- It avoids interoperability problems; and
- It provides a useful structure for organised and centralised groups such as governments, the military, large multinational companies or even well organised industry groups by enforcing practices and policies on CAs
Root CA/Hierarchy working example: Identrus
Identrus[19] is a private New York corporation set up by some of the world’s largest banks to operate a PKI under a root CA for banking operations. It certifies banks as CAs so that they can issue certificates to customers for online transactions. It keeps its CA policies and requirements private, but markets itself as setting an exceptionally high standard in PKI security. A small group of participating banks operate CAs under it.
Despite being well-resourced and having a recognisably useful product – interoperable digital certificates for banking clients – Identrus is yet to firmly establish itself after five years. Identrus’ slow start demonstrates the inherent weakness of the root CA model; it is highly prescriptive and requires a large initial investment. Nevertheless it is the obvious and perhaps the only marketable model for such a high-value application.
Identrus is a careful and competitive project, and has designed several other digital certificate products. It may yet become a significant player with the emergence of larger PKI markets, providing high quality certification services.
Root CA/Hierarchy working example: RegTP
The German national telecom provider, RegTP, is one of several CAs set up as a national root by European governments. However it is cited by a European report[20] as an example of a poorly executed root CA because of its failure to closely observe PKI standards, undermining the interoperability advantages of the root CA model. This failure was blamed on the approach of combining the root CA and supervision/accreditation functions into the same organisation, which left RegTP with no external supervision or auditing.
Root CA/Hierarchy working example: Johnson & Johnson
Johnson & Johnson, a multi-national healthcare company, has set up a PKI that uses over 100,000 certificates, issued to its employees and business partners. It enables a variety of applications in the company’s sensitive operations – such as clinical research, marketing, and financial/legal departments – and at the same time complies with the security standard required by US health data laws and pharmaceutical regulations. This is a widely cited success in the PKI sphere, and has prompted recent activity towards establishing a broader PKI for pharmaceutical corporations.
[19] <http://www.identrus.com>
[20] Refer to footnote 8, page 125.
![[2018 Global Cloud Computing Readiness Scorecard]](/public/ssi/pubs/pub_1.png)
 print this page
print this page sitemap
sitemap rss news feed
rss news feed manage email subscriptions
manage email subscriptions